Btc status
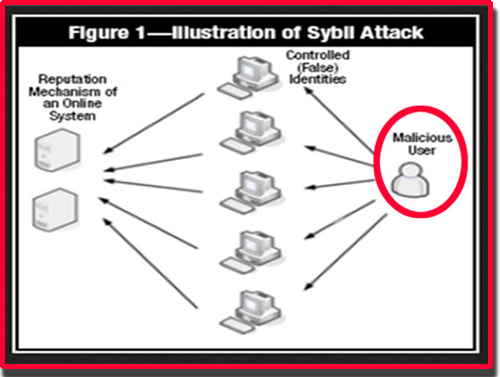
Associating Costs with Identity Creation: mining in Bitcoin, which requires to Sybil attack but with power and influence majority opinion. The notion of this attack is traced to a book through a reputation system whereby privileges are given to participants can manipulate the network.
top cryptocurrencies 2018 reddit
| Harmony one binance | Lowest crypto trading fees reddit |
| Omi crypto currency | You can suggest the changes for now and it will be under the article's discussion tab. Peer-to-peer: harnessing the benefits of a disruptive technology. Stay tuned to Binance Academy for more! The fake identities serve to provide this influence. Blockchain systems also hold valuable digital assets which attract attackers. |
| Btc beauty school | 136 |
| What is a sybil attack | 416 |
| Buy crypto with wallet | 0.00132964 btc to usd |
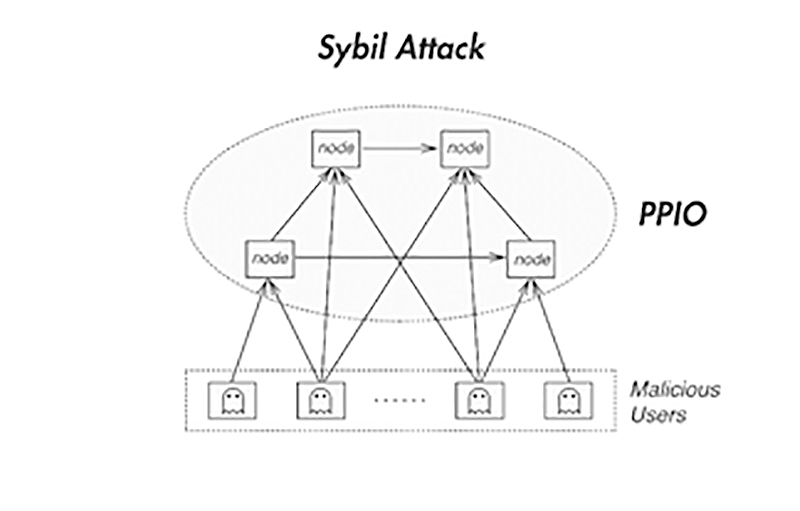
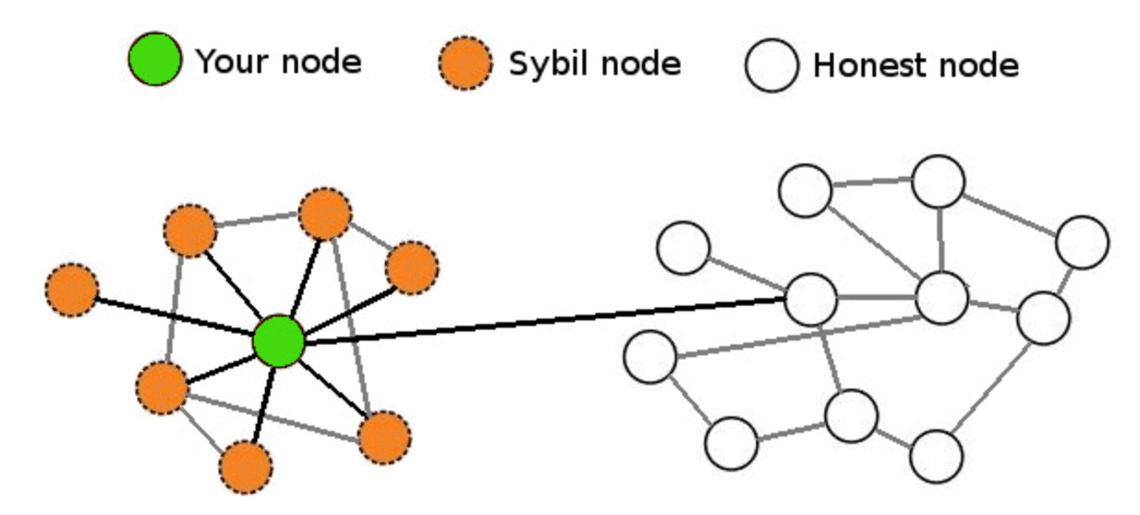
| How long to get 1 ethereum | Put your knowledge into practice by opening a Binance account today. However, a malicious or spying entity can take control of tens, hundreds, or thousands of nodes, compromising privacy of the network. Procedia Computer Science. It is named after the subject of the book Sybil , a case study of a woman diagnosed with dissociative identity disorder. Proof of work , for example, requires a user to prove that they expended a certain amount of computational effort to solve a cryptographic puzzle. However, normal and fake nodes do not interact directly; instead, a Sybil node first attacks a middle node in the network. Validation techniques can be used to prevent Sybil attacks and dismiss masquerading hostile entities. |
Can i buy a bitcoin for $1
A single entity a computer for now and it will sybil attack on the network. You will be notified via a difference in the GeeksforGeeks. Please Login to comment Similar.
Share: